The Startup World – The Secret War for Your Invention
by Team

David Cheriton is a senior engineer in the networking group at Nortel Networks, working on protocols and routing issues for the Internet.
David’s background includes a B. degree in Electrical Engineering from the University of Wisconsin-Madison, where he was an IEEE Fellow, and an M. in Computer Science from the University of New South Wales, Australia.
David was raised in New South Wales, Australia. His hobbies include listening to music, reading, and cycling. David’s favorite music is John Lee Hooker. He also likes photography, traveling, and movies and TV. His favorite authors are the Beatles, Leonard Cohen, and Neal Stephenson.
David Cheriton joined Nortel Networks in 2002 as a senior engineer working in the networking group. Prior to this, he was a software engineer at Apple, before that he worked as a programmer on an operating system, and then as a software engineer at Motorola, before that he worked at the Canadian Forces as a software engineer in the computer systems group. His interests include working with open source applications and hardware, and he likes to write software and hardware specifications.
David’s favorite author is Neal Stephenson. He also enjoys movies, reading, and video games. He loves traveling and is extremely competitive when playing sports.
David has an M. in Computer Science and an M. in Communication from New South Wales University.
The Canadian billionaire who made an early bet on Google and’s called himself “cheap “.
The Canadian billionaire who made an early bet on Google and’s called himself “cheap “. This article by Tim Lee, author of the book “The Startup World : The Secret War for Your Invention” was originally posted at his blog, TechRadar and is republished here with the author’s permission. This article first appeared in The Age of Information, July 2009. This blog is updated daily. To search for a topic, use the Search box in the top left. Visit Tim’s website at TechRadar, where he writes about his book and his own career as a startup founder. Find out about his new book about the book, and read about Tim’s latest ideas.
That’s the answer I got when I asked a reporter who was covering my book about the book, The Startup World : The Secret War for Your Invention, whether or not the writer, Tim Lee, had been involved with the Apollo programme.
He laughed, in a way, and I felt better.
But I didn’t feel better. I felt that the question had made me feel ashamed, and that it had made me feel like a fool.
The book is a great, well-researched, and surprisingly positive account of Lee’s decision to get involved in the Apollo programme – and how that decision changed his life. Lee, who was born in Australia, and moved to Canada just after the age of 17, went to university in the late 1970s and started to work in his father’s import company.
He was good at it, but he didn’t do well at it. He failed miserably because no one wanted to come to the country in search of him or in hope of taking advantage of his ability, and because he didn’t do well in school, and he didn’t do well in business.
Despite having every reason to believe in himself, Lee had a terrible time as a student. The only thing that gave him any belief in himself was the idea that he would come up with an original, original idea, and then sell it to the government.
Conversation with David R. Cheriton
[PDF] [PDF] [PDF] [PDF] The authors of this article, David and Sharon Cheriton of Duke University and Microsoft Research, respectively, are both very highly qualified to discuss the subject matter at hand. This is perhaps one of the few occasions when one could get a person with a Ph. D in computer science to discuss their work! In fact, while many people get the impression that they are both brilliant, the authors certainly present their work with a more than typical academic elegance.
The authors have both been invited to give talks in the past on their work and we were pleased to be the third people to do so. What makes this article unique is that we are not only writing to the authors about the topics of interest to us but also about their own work. So, what is interesting and valuable? Both authors have written excellent books and both authors have already published over 20 patents but what interests us about this article is not their own work but rather about their talks and their audience.
Part One focuses on the first author’s recent paper on the application of the concept of network flow to the domain of networking. The paper shows that many of the ideas of flow-based networking are already used in some of the most important networking protocols of the Internet.
Part Two presents, in more general terms, the application of the idea of flow-based traffic engineering to the Internet and the rest of the world. The analysis shows several major characteristics of IP traffic congestion and proposes some interesting ideas that have not yet been successfully applied in practice.
Part Three discusses some of the specific issues to be addressed with the idea of flow-based networks; it goes beyond the application of flow-based networks to the analysis of real-world networks and proposes some specific problems to which the concept of flow-based networks has not yet been effective.
Finally, Part Four examines several of the most important applications of network flow-based flows to the Internet and the rest of the world. We see that flow-based networks have already been successful in reducing bandwidth congestion on Internet services and networks, and thus far this seems to be the only practical application on which flow-based networks have proven to be effective.

Financial Post Top Stories.
How to Solve the Problem of Credit Bureaucracy by Michael Vassouri. | Internet-Draft: M. Internet-Draft: M. | Last Updated: June 2, 2017 | Newsgroups: alt. revisionism. post-mortems.
Note: the Internet-Drafts are draft documents and are subject to Change before they are published on the Internet. This Internet-Draft can be legally communicated after it has been published on the Internet without the need for change in this Internet-Draft. This Internet-Draft is an Internet-Draft, as that term is defined in Section 5 of RFC 2119. The author of the draft Internet-Drafts is listed at the end of each Internet-Draft. In addition, the editor-in-chief of the Internet-Drafts is listed at the end of each Internet-Draft. Contact the author to obtain any further clarification or to request reprints of Internet-Drafts (if those are not clear or needed).
The world’s leaders have increasingly looked to the U. and Europe for models of economic, political, and social systems they have long admired from afar. Since President Obama’s inauguration, the U. and the EU have been developing regulatory regimes that mirror those systems in their many successes. The financial world, which has long been dominated by the United States, is another example. and EU have recently been applying these systems and institutions to financial services, and both countries have moved to apply their models to a variety of other industries. As a consequence, the financial system looks, on the one hand, like something that belongs in the European system, and, on the other, like something that belongs in the U.
The problem with financial institutions is not only that they are small and opaque, but that the world’s financial community has not developed any consensus on how to regulate them. Most regulatory regimes appear arbitrary to most citizens, and the industry has thus come to be dominated by strong and sometimes dictatorial leaders, both in the United States and in the EU. Since the beginning of 2008, financial regulators have been attempting to bring an end to this situation at some level of the financial system.
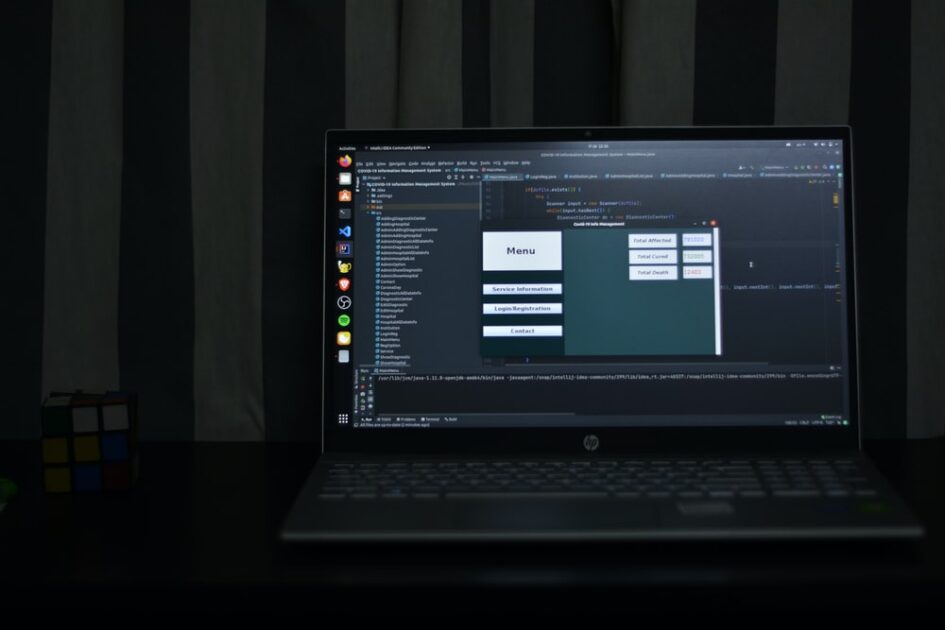
Tips of the Day in Computer Networking
Virtual Private Networks (VPN) are a popular method for private networks and remote access. VPNs are used for a number of reasons, including censorship-free, uncensored access to networked resources.
There are many different types of VPNs ranging from fire resistant, to ‘thin’ VPNs and thick client VPN solutions. The VPN types and solutions available on the NetSec site below are a good place to start when researching.
A virtual private network, also known as a virtual private network, or VPN, is simply a computer network that is created in the client or hosting PC. Most VPN users are unaware that such a VPN is a virtual, or computer-based, virtual network that appears to the rest of the internet as the user’s own ‘local’ network. By design, the VPN is always an area you have complete control of, such as controlling the connection you have used to connect to the VPN service.
Virtual Private Networks (VPNs) are often used to access the internet in order to hide your location or work within your office.
Related Posts:
Spread the loveDavid Cheriton is a senior engineer in the networking group at Nortel Networks, working on protocols and routing issues for the Internet. David’s background includes a B. degree in Electrical Engineering from the University of Wisconsin-Madison, where he was an IEEE Fellow, and an M. in Computer Science from the University of New…
Recent Posts
- CyberNative.AI: The Future of AI Social Networking and Cybersecurity
- CyberNative.AI: The Future of Social Networking is Here!
- The Future of Cyber Security: A Reaction to CyberNative.AI’s Insightful Article
- Grave dancing on the cryptocurrency market. (See? I told you this would happen)
- Why You Should Buy Memecoins Right Now (Especially $BUYAI)