Cyber Professional | Computer Security
by Team

Cyber professional | Computer Security. Article Date: December 2016. Author: Shrikant Mohan | Shikant Mohan is a cyber professional and a computer security researcher. His area of interest is the cyber security and the attacks on computer networks.
A report in Telegram case modified by the court which is directed towards the investigation agency, the Enforcement Agency, the Central Bureau of Investigation. The case has been referred for further investigation to the Cyber Criminal Squad of India. Read the report in full.
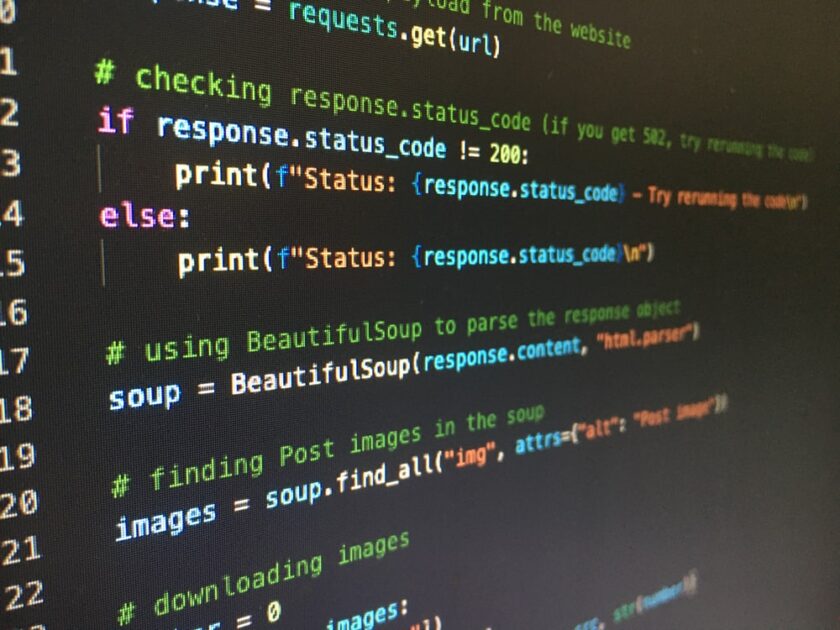
The article has been published by Computer Security and security researchers to explain the attack scenario of criminals. The article focuses on the way the criminals are using social media like Twitter, Facebook and LinkedIn to communicate with each other. Using this medium, criminals are able to steal or create many accounts like bots. It is a popular way of cyber crime.
In this short article, I analyze the report sent by the Enforcement Agency on the Telegram case. I intend to explain the attack scenario in this case. For further information, please visit the original report.
The Enforcement Agency sent an order to Telecom Regulatory Authority of Singapore (TRANSPARENT) for a report. The Enforcement Agency sent the Telegram message to the Telecom Regulatory Authority of Singapore (TRANSPARENT) on November 28, 2016 demanding for a report from the Enforcement Agency as to how the government is trying to prevent and investigate cyber crimes. It seems that one of the questions asked by the Enforcement Agency was how the government is trying to detect and investigate cyber crimes. The Enforcement Agency sent a report to TRANSPARENT on the same day (November 28, 2016). The report contains the details of the security measures, such as how the government is trying to detect and investigate cyber crimes, such as spearphishing, phishing and cyber attacks. It also details the different kinds of cyber crimes which are covered in details.
The Telegram message that the Enforcement Agency sent was a public message. Therefore, anyone can access it with a computer. However, the Enforcement Agency sends the message to TRANSPARENT for its approval. The Enforcement Agency sent the report to TRANSPARENT for its approval. It is not allowed to share the report which has the content details and also the approval of the court which is the Enforcement Agency.
NIA case sheet in Antilia bomb case
In 2014, the Internet Research Center (IRC), a website used by Russian operatives, was revealed to have a sizable botnet of infected devices. These bots were reportedly installed against the Department of State and other agencies. Two months later, the Russian government began to release more details on what they had found on IRC, including the location of certain servers, the IP addresses of the individuals who were running them, and more. As an example, IRC operators were reportedly targeting a Pentagon computer network that was used to respond to requests for intelligence from Congress and the media. Shortly thereafter, IRC operators were found installing malware on some of the computers of the Department of Homeland Security (DHS), the Department of Justice (DOJ), the Federal Bureau of Investigation (FBI), and the Department of Defense (DOD).
At the cancellation of Nita Ambani’s planned visit to Gujarat, a prank was announced.
A prank called “Rashtraya Nita Ambani” was organised among activists of BJP and NITI Aayog. The prank took off against Gujarat’s Chief Minister NITI Aayog on July 4, and the prank became viral, and eventually caught the attention of other newspapers, television channels, and media houses all over the country. The prank was then distributed in Gujarat’s Hindi and English media, which called it Nitaam, Nitaank, Rashthak Nitaam, etc. It even made its way to the topmost levels of the media industry in India. It is a great prank and shows the gullibility of the people of Gujarat. This prank has become immensely interesting for Indians. Article Source: www.
At the cancellation of Nita Ambani’s planned visit to Gujarat, a prank call was made, and a prank was created which has gone viral all over the country. It is believed that the prank called “Rashtraya Nita Ambani” was organised by people of BJP and the India Today group (NITI Aayog). The prank took place in Gujarat’s Capital on July 4, 2018, and is now viral. This is a great prank and shows the gullibility of people of Gujarat. Article Source: www.
Nita Ambani, the country’s richest woman, was slated to visit Gujarat’s capital on July 4, 2018. She was scheduled to spend around three days in the city. By the end of the month, reports emerged that Nita Ambani has cancelled her planned visit and was instead making a visit to Delhi. Her son, NITI Aayog member Sanjay Agarwal, said that the government had a “planning to divert attention away from Gujarat”. Article Source: www.
Nita Ambani has a very lucrative business empire, running from her personal residence to other states. She is the richest woman in India, and her business empire is not a secret.

On the Antilia scare to CP Mumbai.
Abstract: On the Antilia scare to CP Mumbai, May 2018.
It is a well-known fact that a large number of attacks are carried out by cyber criminals by exploiting vulnerabilities in various software systems installed on a system. In order to evade detection, cyber criminals first make changes in the operating parameters before creating the shellcode that will get loaded at run time. To protect systems from being attacked, security engineers often use various techniques to mitigate such attacks. For example, most of the security tools are written in an un-patched version of Microsoft. NET Framework.
As many systems are compromised by various threats like SQL Injection, Cross-site scripting, Cross-site request Forgery, and many others, it is impossible for hackers to fully evade detection. On the contrary, it is very difficult to get a clear idea about the real cause behind the attack. Hence, it is very essential to analyze the details of the attack to be able to effectively mitigate it.
This paper focuses on the issues related to the security vulnerabilities in the. NET Framework used by the Antilia malware which was released in May 2018. After analyzing the source code of Antilia, we found several vulnerabilities that existed in the. NET Framework used by the malware.
Following is an overview of the main characteristics of the Antilia malware that is known to cause various security vulnerabilities in various software systems.
Antilia is a modified version of the infamous Dridex malware that originated in Iran. Unlike the original version, the Antilia malware has been adapted to be compatible with Windows 10 and Microsoft. NET Framework 8. It has also been written in C# language, which is a popular C# language used in Microsoft products. Since Microsoft has released a. NET Framework version, Antilia could use the latest development version of the. NET Framework.
On the Antilia scare to CP Mumbai.
The Antilia malware comes with a unique feature called the Antilia scare to CP Mumbai.
The Antilia scare to CP Mumbai is a novel technique that gives the attackers the control over the machine that they operate and does not require the attacker to control the operating system.
Tips of the Day in Computer Security
If you have experienced a hacking incident and you’re hoping you can prevent your own or your company’s security from being compromised, you’ve probably noticed a few signs that the security infrastructure in your business is unhealthy.
Your database is aging. Your security controls are not effective. You’re receiving an influx of phishing emails and phishing phishing phishing emails are increasing your risk of being victimized.
In this article we will talk about 5 signs that your security infrastructure is unhealthy and also point out the 3 things you can do about it.
Your database contains all the information that your company has collected over the years, such as contact lists, credit card numbers, employee names, payroll information, and much more. All of these data points are valuable and should be collected and stored and analyzed to ensure that security of your business is implemented.
Related Posts:
Spread the loveCyber professional | Computer Security. Article Date: December 2016. Author: Shrikant Mohan | Shikant Mohan is a cyber professional and a computer security researcher. His area of interest is the cyber security and the attacks on computer networks. A report in Telegram case modified by the court which is directed towards the investigation…
Recent Posts
- CyberNative.AI: The Future of AI Social Networking and Cybersecurity
- CyberNative.AI: The Future of Social Networking is Here!
- The Future of Cyber Security: A Reaction to CyberNative.AI’s Insightful Article
- Grave dancing on the cryptocurrency market. (See? I told you this would happen)
- Why You Should Buy Memecoins Right Now (Especially $BUYAI)