Computer Hardware and Computer Software
by Team
What you see is not always what you get.
Computer Hardware. Computer hardware and computer software, the manufacture, distribution, and use of, are in the same business. Computer hardware, such as integrated circuits on printed circuit boards (PCB’s) may be composed of plastic, glass, or other materials in a variety of shapes, size, forms, and configurations. In other words, computer hardware and computer software are made by the same people, and are inextricably linked in the computer and information processing industries. Computer hardware and computer software in the form of integrated circuit (IC) chips and computer boards, for example, are used for data transmissions, data processing, electronic products, and data networking throughout the world.
The Internet is a network of networks. The networks are the computers that form the network. The computers are the hardware that is the building material of the network. The hardware is the actual computer that is the most basic element in the network. A network is the set of computers that are connected to each other.
Electrical engineers use computer hardware and computer software to make the circuitry of an integrated circuit (IC). The ICs are the most common form of the computer hardware.
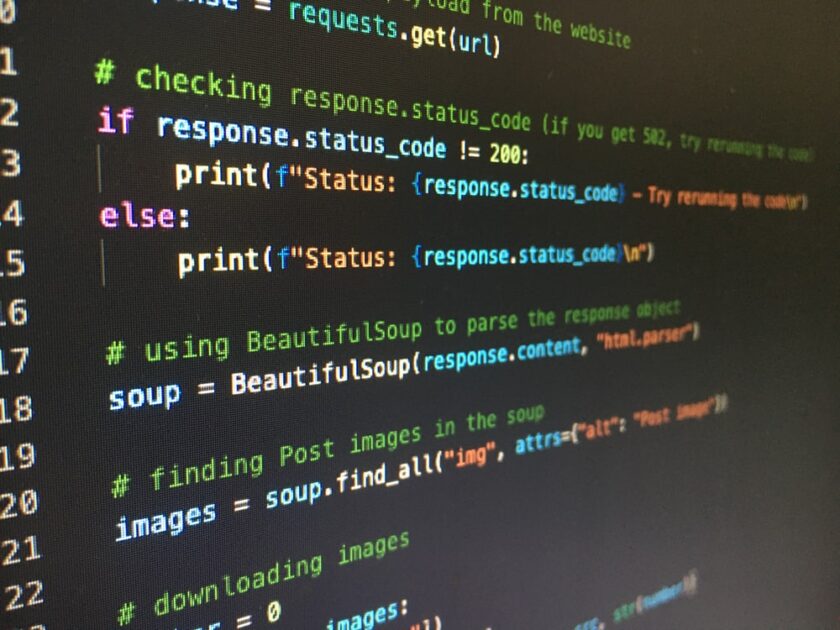
A computer software is a program that runs on the hardware. For example, the program known as C. There are computer software programs and there are computer software libraries which hold computer software programs. Computer software is sometimes referred to as manuals, manuals, manuals, manuals, and manuals.
Computer hardware is used to make the circuitry of computers (hardware) in the form of integrated circuit chips and computer boards, for example. The circuits are the parts of integrated circuit chips that make up a piece of computer hardware. Chips are small, usually about 1 millimeter in diameter, and rectangular in shape. They are made of semiconductor material and are made to connect together. Computer hardware is a collection of all of the chips contained in a piece of computer hardware, or a set of connected chips.
The electrical engineer or electrical engineer’s helper is the person who makes a circuit in a computer. He or she may have to cut up the circuit boards to form the wiring that connects the components to each other, or the person may need special tools because he or she is working with very small chips.
When two pieces of computer hardware are joined together, they are called a circuit.
The FBI search for the home of Gabby Petito’s fiancé Brian Laundrie.
The FBI has found at least eight items that have been stolen from Petito’s home. One of these items was found by an FBI agent on September 24, when the agent was searching for a computer that was allegedly stolen on August 11, but was not found until more than a month later, according to a search warrant application for a residence that was obtained by the Daily News. A few days before the FBI took possession of this computer, it was being sent from a California address to the FBI via the Internet. The FBI has now located the computer and found that it is registered to a third person who is not known to the FBI. The FBI also found items belonging to a woman who was not Petito, but who is believed to be Petito’s friend, or as the search warrant states, a co-conspirator. The FBI has turned over eight items to the Manhattan District Attorney’s office, and several of these items are still in the Metropolitan Correction Center. These items, which include a laptop, a video camera, a video tape player, a computer monitor, and a video game console, have been turned over to the Manhattan District Attorney’s office. The items also include a cell phone and a cell phone charger. The items discovered by the FBI are a camera that was recovered from the car that was used in the Petito murder, and a video camera and video recordings of a police officer. The agents believe these items all belonged to Brian Laundrie and would be used in an attempt to obtain his fingerprints for the investigation. The FBI also has found documents relating to a stolen computer allegedly belonging to Laundrie. The FBI is in possession of the following items: A computer monitor; a laptop computer; a video camera with a video memory card; a cell phone charger; various documents relating to the investigation of a case in Massachusetts; a video tape recorder with a video memory card; various documents relating to the investigation of a computer in California; a laptop computer; a video camera with a video memory card; and a video tape recorder with a video memory card. The FBI also has found documents relating to the case in Massachusetts. The documents include, among other things, a search warrant and a letter relating to the kidnapping, torture, and murder of a young girl. The documents also include letters to the FBI.

Laundrie’s home was searched after leaving home.
Laundrie was taken to police custody after her son discovered a purse on her property. Laundrie was then taken to the police station where a photo of her was taken. The purse was turned in to police with a warrant on it, and a warrant was also issued for her house. The police report shows that the purse in question contained cash and another purse containing a large quantity of cash. Laundrie was subsequently arrested. Laundrie was later booked into the St. Lawrence County jail and charged with possession of a controlled substance.
On June 4, 2003, at approximately 7:40 p. , Laundrie was arrested for DUI in St. Lawrence County Court, in connection with another offense.
On November 9, 2003, in connection with another DUI offense, Laundrie was placed on probation for 12 months and ordered to complete one year of community service during her probationary period.
On October 4, 2004, at approximately 6:52 p. , Laundrie was arrested for possession of marijuana.
On June 2, 2006, in connection with another arrest, Laundrie was placed on probation for a period of one year, and was ordered to complete 6 hours of community service during her probationary period.
On January 25, 2007, in connection with another DUI offense, Laundrie was sentenced to probation and ordered to complete two years of community service.
On June 1, 2007, at approximately 4:00 p. , Laundrie was arrested by the police after her husband returned from a trip to Florida; Laundrie was then placed into the police station. The police report shows that Laundrie had been using drugs since 2003. The police report shows that Laundrie had received numerous DUI tickets in the last year. The report also shows that Laundrie admitted to the officer that she had a prescription for Vicodin, Oxycodone, Buprenorphine, and Fentanyl.
On October 24, 2007, in connection with another DUI offense, Laundrie was sentenced to 10 days in jail and placed on probation for one year.

Video of a van with Florida plates in the Bridger-Teton National Forest.
When a camera isn’t enough, a hacker can also shoot video from inside your computer. The video below is from a hacker who was able to get a GoPro Hero8 plus camera to record an episode from the “Breaking Bad” series on the Netflix. The series was the inspiration for the hacker’s project. The GoPro has the capability of recording up to a 1080p video at 60 frames per second. His GoPro was able to make this video available to his website, www. captivevideo. The video can also be viewed on www. The original source can be seen in YouTube. The GoPro is very easy to find online. You can also find videos of the camera on YouTube. This video was recorded by a guy named Chris “Chimp” Rance. Please note the link above is for the actual video uploaded on the Pirate Bay, not the hack. There is also a video of the same incident of a man who was kidnapped by the pirates. The video above is of one of the kidnappers. The video below is of a hacker who tried to steal a Sony PlayStation 4. There is also a video of the same incident of a man who was kidnapped by the pirates.
In the video above you can see a GoPro Hero7 Plus (which is the camera used by the hacker) recording the episode of “Breaking Bad” on the Netflix. You can also see a GoPro Hero7 Plus (the camera) recording the episode of “Breaking Bad” on the Netflix.
The hacker was able to record this as a 1080 quality video that was recorded on a GoPro Hero7 Plus (the camera) with the remote control on. The video was recorded from inside the computer.
The hacker’s hack isn’t the only one of its kind. Another hacker was able to create a recording with a Samsung Galaxy Note 4 in the U. The video below shows the “Breaking Bad” hacker’s video that was able to be captured on the Samsung Galaxy Note 4. The video was also recorded using the camera attached to the video phone.
“The video was shot from an iPhone and the phone’s camera.
Tips of the Day in Computer Hardware
Microsoft’s Windows OS and the Linux 2. 0 OS from Red Hat.
Linux and Windows are both well-known on the PC gaming scene. But with the latest, Windows 7 and Linux from Red Hat and the upcoming Linux edition of the Mac OS from Apple, the two have come to the same time in the gaming PC landscape. How well will they perform? This is where you will look to see what they can offer in terms of gaming and how well they work for the average consumer.
One thing that is always present in these sorts of comparison studies is that many PC gamers are gamers first and Windows and Linux gamers are gamers second. While this does not mean that the two types are inherently different, that they are not the same has been shown when it comes to hardware. As the title suggests, the topic of comparison can be a bit of an eye opener for everyone looking to see which gaming PC is going to satisfy the average consumer.
This is also the time when the two gaming platforms come down to the hardware.
Related Posts:
Spread the loveWhat you see is not always what you get. Computer Hardware. Computer hardware and computer software, the manufacture, distribution, and use of, are in the same business. Computer hardware, such as integrated circuits on printed circuit boards (PCB’s) may be composed of plastic, glass, or other materials in a variety of shapes, size,…
Recent Posts
- CyberNative.AI: The Future of AI Social Networking and Cybersecurity
- CyberNative.AI: The Future of Social Networking is Here!
- The Future of Cyber Security: A Reaction to CyberNative.AI’s Insightful Article
- Grave dancing on the cryptocurrency market. (See? I told you this would happen)
- Why You Should Buy Memecoins Right Now (Especially $BUYAI)