Computer Security in the Cloud
by Team

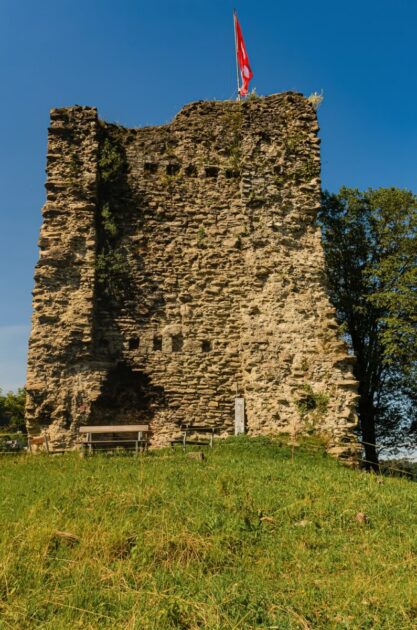
Windows Hello Face Authentication.
Computer security is the topic that interests me the most. It has become such a critical element of every computer system that it is quite hard to ignore the security implications in an ever changing internet world. The computer security world has a huge presence on the internet on a variety of platforms. These platforms include, but are not limited to, social media, messaging apps and messaging apps that are native applications. This means that we are in a digital world of computers interacting with each other in a peer to peer fashion. Many of these platforms have been built to help individuals who want to hide their identity by changing their user agents to hide their IP addresses. The reality is that these platforms have been constructed to help individuals to become more anonymous as they can easily hide behind social media platforms. The reality however is that the best defense is good offense. We are all aware of the numerous exploits that are taking place on these platforms, and as we have heard so many of the people who have been affected by them, there is a high level of danger of getting your identity stolen and your money being stolen in the name of a social network.
There should be a system in place when it comes to security in the cloud, however, we have been asking many questions on this issue and it is because of these questions we have been asked to build an architecture. We have received many responses from the different platforms and also for example, Microsoft have said that they will be working on some type of system in terms of security in the cloud. I wanted to take the opportunity and discuss how this should look like on a number of platforms in relation to the computer security world and how it should look like on the cloud, and how it should be a system that is being built.
The computer security world has many things to talk about and discuss. I will discuss about just two of the biggest aspects and that is how to secure a cloud platform, and then I will go into a bit about how a system should be built. The first will be Microsoft’s Microsoft Azure. The second will be our third party which is from a company called RSA Security and I will talk about how they build these systems so that they do not have to build them by themselves.
Occasionally wearing certain types of glasses.
Computer Security.
John Wiley & Sons Inc.
The author has made every reasonable effort to ensure that the information contained in this book is correct at the time of publication. However, no responsibility can be accepted for any loss or damage caused by the use of this book. Neither the publisher nor the author shall be liable for any loss of profit or any other commercial damage, or any other commercial injury, resulting from the use of any information contained in this book.
John Wiley & Sons Inc.
One of the most fundamental features of information security is the requirement that all information that an organization receives, processes, or stores must be of a type and/or caliber that is not only considered and accepted, but also that information that the organization receives, processes, or stores is not being used in an improper or dangerous manner. The requirements here are not technical definitions of what we mean by a bad use of information, but rather a recognition that a user of information will not be free to use or misuse information improperly. For example, an employee who is not in good shape will not be able to send a computer virus because an access request to the computer network will not contain information that reveals that the employee has an infection. Similarly, a programmer who has not been paid to use source code is not permitted to send viruses because the information provided in source code is not of a type and/or caliber that would identify an infection. Instead, it is important to consider that the programmer is using information that could be an infection because the information on the computer that is being made available to the programmer is not subject to a good or bad use.
Even when the information that is provided is of a good or bad type and/or caliber, the person receiving the information could in some instances use that information for inappropriate purposes without giving that information the proper treatment.
Should External Cameras be forbidden?
Should external cameras be forbidden? | Computer Security.
There are many things that are wrong with the current state of video surveillance.
The lack of a clear distinction between physical and digital video surveillance.
A lack of clear distinction between physical and digital cameras.
No unified standards for surveillance equipment and data formats.
A lack of ability to handle data-loss if the equipment fails.
Many cameras, regardless of manufacturer and camera model, have the same video resolution, which has led to a lack of capability in terms of detecting “false positives” for potential malicious use. This means that potential abuse will occur as well.
The lack of a standardized mechanism for capturing and displaying the recorded video has also led to a lack of a unified way for people to communicate and share information. People are sharing pictures of what they’re doing in the open, and most don’t see what is being captured from them unless they explicitly look on it. It is also difficult for people to figure out what they are seeing.
The lack of a strong centralized authority to oversee the video surveillance system, as well as the lack of standardization between different vendors and cameras, have also led to a lack of unified data formats and a lack of clear separation between data formats.
The lack of any kind of centralized authority is a common problem across the enterprise as well as the security industry. The problem goes beyond data formats and video format. The fact that there is such a disparity across different parts of the security industry means that there has been an inordinate amount of confusion going on with regard to what is actually important and what isn’t. There has also been an imbalance within the enterprise as well, and many organizations are not able to keep up with the amount of information that is being captured from various sources.
It is important that anyone involved with video surveillance should know the importance of centralized authority, so that we can all share and communicate, and find common ground and find areas of disagreement and confusion. When centralized control is not in place, it becomes easy for hackers to take over the system.
Security experts have been debating this issue for years.
Tips of the Day in Computer Security
By Michael S.
I am frequently asked why we do this. The answer is simple: so many people work on our platforms. I’ve been involved in this industry for over 35 years. We have to address this problem.
We think this answer is so obvious and so simple, that you might not be able to understand it. But you’ll find it simple in fact.
There are three reasons hackers hack. The three reasons are different, and some of them may not seem related to each other. The first reason is to get money, and the second reason is to steal information. The third reason is to make trouble for law enforcement.
We all know that hacking is illegal, and we all know that hacking can be harmful.
There are a few exceptions where hacking is legal. For example, stealing information from someone isn’t illegal, but it’s a very different matter from hacking someone to get money.
There is a third reason.
Related Posts:
Spread the loveWindows Hello Face Authentication. Computer security is the topic that interests me the most. It has become such a critical element of every computer system that it is quite hard to ignore the security implications in an ever changing internet world. The computer security world has a huge presence on the internet on…
Recent Posts
- CyberNative.AI: The Future of AI Social Networking and Cybersecurity
- CyberNative.AI: The Future of Social Networking is Here!
- The Future of Cyber Security: A Reaction to CyberNative.AI’s Insightful Article
- Grave dancing on the cryptocurrency market. (See? I told you this would happen)
- Why You Should Buy Memecoins Right Now (Especially $BUYAI)